Battle lines are being drawn. The stakes could never be higher, the very future of how we all interact online is in our hands. It was so simple when everyone was silo’d onto a few corporate controlled platforms. Now, there are new platforms that aren’t merely controlled by a single entity, they are interoperable with each other, meaning that each system is composed of compatible units.
Will one system entirely dominate the others? Will “super-nodes” grow to dominate the entire ecosystem, leaving us with big tech tyrants yet again? How will you ensure that communications networks aren’t used as tools to shape the discussion, rather than support it?
Awaiting the peer-to-peer utopia
Currently, we’re not quite able to jump straight to a private, secure and free-as-in-freedom peer to peer network. There are a variety of challenges in attempting to create a pure peer-to-peer ecosystem that get in the way. A peer-to-peer ecosystem that relies on participants using locked-down and controlled smartphones has limited usefulness. On the other hand, peer-to-peer file-sharing networks have maintained their robust existence as they are build on top of powerful machines with lots of bandwidth and storage.
We can’t escape the fact that hardware is a critically important part of the technological landscape. People’s own technical skill and the capabilities of their hardware have a profound impact on what possibilities can emerge. There are real trade-offs when trying to move away from a client-server model. This is because servers are useful and efficient. Different participants may want more or less resources assigned to particular tasks, and using specialized hardware for the task goes a long way.
There are also privacy risks when it comes to peer-to-peer connections. Some protocols still will require a server to set up connections between peers, and unless you’re using an anonymization network like Tor or I2P you’re divulging information about you to other peers. This is why there is still a long way to go before truly peer-to-peer systems will be used as the standard.
The Server to Server paradigm.
This doesn’t mean we can’t meaningfully decentralize. It’s possible for people to run servers for themselves as well as others. The people using them gain most of the advantages of centralized systems, like being able to connect from thin-clients like smartphones.
You can then add real interoperability by using an open protocol to allow the servers to act as servers for each other. With a Server-to-Server layer, these systems have the advantage of being parts of a larger whole. Often these systems are called federated because they work as networks of communities.
This allows new protocols and systems to scale as well as the internet itself. Having a server-to-server mechanism allows for an incredible amount of flexibility. Maybe some servers respond to all the others, maybe some of them only respond to ones they know. Everyone could eventually be situated with their own preferences without impacting others, all while still having an interoperable means of connecting.
Bridges
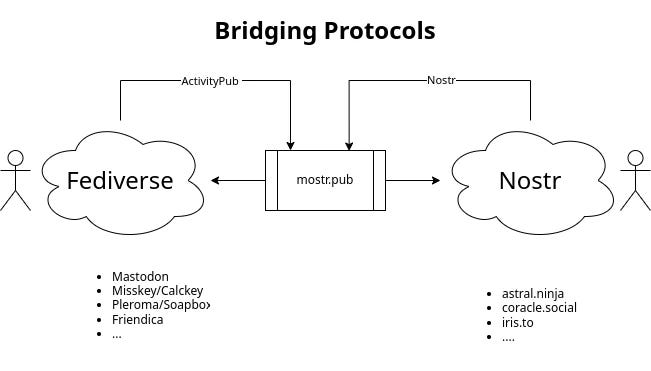
Once there is an open server-to-server protocol in place, it’s easy for different systems to be bridged to each other. Either systems can adopt the same server-to-server protocol (federation) or they can translate from one protocol to another (bridging).
Bridges have been used on matrix to allow people to control all their chat applications from a single account. Any open protocol can be bridged to bring people together.It’s a powerful technique that means that no single protocol has to dominate, instead they can cooperate.
Trade-offs
There are large differences to using different ecosystems. People may prefer something that could be decentralized but is still quite controlled like Blue Sky, or they may want to build custom software to only use protocols in deliberate ways. It’s a wide spectrum, and some choices have bigger impacts than others.
Things worth considering are:
Is the protocol open and allows permissionless participation?
Does the protocol allow you to store information on your own machine, or one under your control?
Is the software free from unwanted or harmful dependencies?
Broadcast systems
If you’re trying to get information out into the world, privacy may not be the highest priority. You’ll still want to be secure, you won’t want to be credibly impersonated, but you may not need perfect anonymity or to encrypt messages. A simple static website suits this purpose, but so does a profile on a well-run and popular social media service.
Fediverse
The fediverse has the potential to be a truly meritocratic digital town square.
There are many community-run or self-hosted servers that operate without algorithmic manipulation or ads. Each user either runs or joins an instance that will host their content as it’s shared with others.
Get started: https://jointhefedi.com/
Popular Servers: Soapbox or Mastodon and many more..
Nostr
Nostr is a simple protocol with lots of new clients and features being built. It replaces the concept of a “home server” with many inter-changable relays. The primary advantage of this is that it prevents server administrators from being able to block people on behalf of other users. As long as two nostr users share a relay they are able to communicate. Some nostr communities have setup paid relays.
Get started: https://nostr.com/get-started
Project: https://nostr.com/
Popular Client: https://iris.to
Popular Relay Software: nostream
Private Systems
When having private communications with friends/family or even co-workers it’s great to have systems away from prying eyes. It’s helpful to have a free and open protocol that people can communicate with you privately, that doesn’t rely on sharing infrastructure. End-to-end encyption helps protect users on different servers from prying-eyes.
Matrix
Matrix is an excellent chat protocol that supports large rooms as well as direct chats. As of now, video rooms are now in open beta.
Get started: https://matrix.org/docs/projects/try-matrix-now
Project: https://matrix.org
Popular Client: https://element.io
Popular Server: Synapse
XMPP
XMPP is another federated chat protocol. It’s fast and efficient and has been used for quite some time now.
Get started: https://xmpp.org/getting-started
Project: https://xmpp.org
Popular Client: Gajim
Popular Server: Prosody
Making your choice
It’s up to you! It’s worth trying different things out to see what works well for others. Some may just stick with signal for convenience, others may use delta chat because it can be used on top of e-mails people already have. Whatever you can do to take control of your own information and computing can go a long way.
Check out this conversation I’ve had with
on Rounding the Earth about how to think about different approaches to keeping your information safe.Whatever you do, it’s important to know why you’re choosing one system over another. It may be more effort, but a little change can go a long way when it comes to keeping your information out of the hands of adversaries. Once you have something that works well for you, it becomes easier to share those advantages with others.







Thanks.